Data breaches have become more common than we’d like, and this frequency is attributed to a wide gamut of reasons that span from sophisticated strategies used by hackers to poor security practices of organizations.
One technology or practice that’s seen as a key strategy to protect your data is encryption. According to the Ponemon Institute, robust encryption strategies help businesses to save an average of $1.4 million per attack. But at the same time, not all organizations currently use encryption and this is evident from the fact that more than seven million unencrypted records are compromised every day.
There are many reasons for this gap in understanding the benefits and implementing them. In this article, we will focus on the implementation aspect. Encryption is often seen as an expensive and arduous process, but that’s not true, thanks to the availability of endpoint encryption software solutions.
What are Endpoint Encryption Software Solutions?
Endpoint encryption software protects your data at the endpoints where they are accessed. What this essentially means is that a user who wants to access data must have the decryption key to decrypt the data and use it. This mechanism weeds out random hackers because they can’t use the data even if they manage to hack into the system. It also ensures that only authorized people who have a valid decryption key can access the data from these systems.
Many endpoint encryption software solutions are available today, and here’s a brief look at some of your top choices:
- ManageEngine Endpoint Central – EDITOR’S CHOICE This tool simplifies the process of managing Windows Native BitLocker and supports the deployment of granular policies to improve security and compliance. Start a 30-day free trial.
- Symantec Endpoint Encryption This tool encrypts all files on the hard drive to provide high levels of security for your information. It can also encrypt hard drives and removable media and supports a wide range of operating systems such as Windows and Mac.
- Virtru An advanced data encryption platform that keeps your data safe at all times, regardless of where it is stored and how it is shared or transferred.
- Sophos Central Device Encryption This is full-disk encryption software that works well on both Windows and macOS. Its web-based management eases the setup and maintenance processes as well.
- Check Point Harmony Endpoint This tool offers centrally enforceable encryption of all drives and removable media to protect your sensitive data from losses and thefts.
- Trend Micro Endpoint Encryption This platform encrypts data across a wide range of devices, including removable media, to prevent unauthorized access to your sensitive data.
Let’s take a detailed look at each of these tools to help you make an informed buy decision.
The best Endpoint Encryption tools
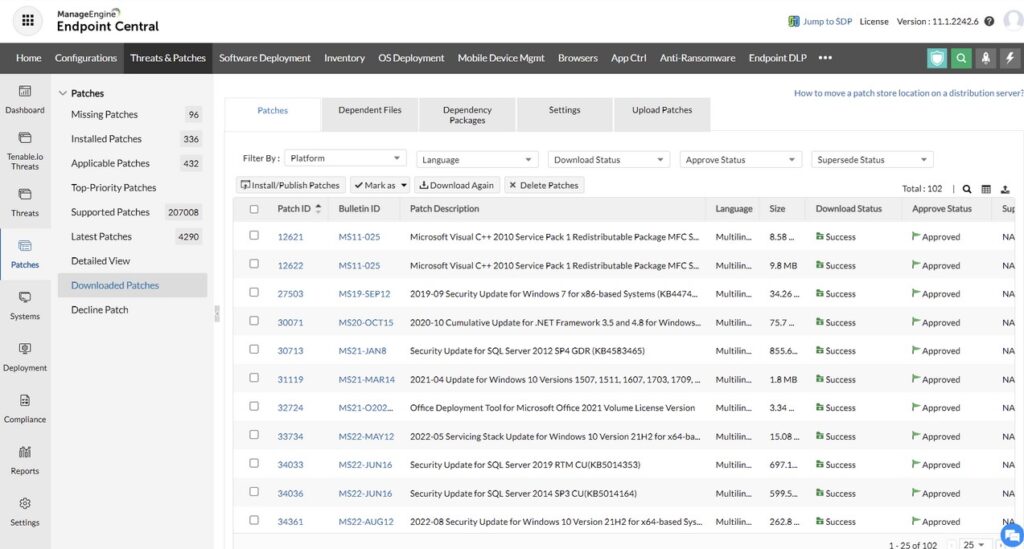
1. ManageEngine Endpoint Central – FREE TRIAL
One of the features of ManageEngine Endpoint Central is BitLocker management, which safeguards data through encryption. It is ideal for configuring the Windows Native BitLocker, Trusted Platform Module (TPM), and other additional protector settings through a single console. With such centralized control, you can automate many activities like key generation, deployment of granular polices, and more.
Key Features:
Here are the most important features of Endpoint Central’s BitLocker management.
- Policy deployment: With this tool, you can seamlessly deploy security policies for your unique encryption requirements. It’s also easy to map policies with custom groups and target applications.
- Monitoring: You can control encryption, keys, and other security-related configurations through a single pane, making it easy to monitor their status and performance.
- Compliance: Endpoint Central ensures compliance with the required standards. It also generates reports and simplifies audit preparedness.
- Security: Protects your network from unauthorized data breaches due to poor and insecure key handling.
- Dashboard: Its comprehensive dashboard provides real-time insights into security.
Why do we recommend it?
ManageEngine Endpoint Central is a comprehensive security tool that enables you to make the most of Windows BitLocker. It comes with many automated features, like recovery key generation, seamless key rotation, and more. Its compliance reports and the ability to implement security policies organization-wide with a single click are other compelling reasons to use this tool.
Who is it recommended for?
This tool is best-suited for organizations that use a Windows environment, Also, it is ideal for organizations that handle sensitive data and must meet compliance requirements.
Pros:
- Reduced risk: Minimizes security risks across the organization.
- Audit readiness: Enables organizations to be prepared for audits with the right access controls.
- Maintains uniformity: The ability to deploy encryption policies ensures uniform security is maintained throughout the organization.
- Intuitive dashboard: Its intuitive dashboard provides centralized control and visibility.
Cons:
- Windows environment: It is suited only for Windows environments.
Overall, Endpoint Central is a good choice for organizations that want to improve their security posture through streamlined encryption and granular policy deployment. Start a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Endpoint Central is our top recommendation for encryption software because it augments Windows BitLocker with features like automatic key recovery, seamless key rotation, and centralized management. With such features, you greatly reduce gaps in encryption and the resulting security breaches. Additionally, it supports compliance with existing standards and generates the reports needed for audits. Using this tool, you can also deploy granular policies easily.
Download: Start a 30-day FREE Trial
Official Site: https://www.manageengine.com/products/desktop-central/bitlocker-management.html
OS: Windows
2. Symantec Endpoint Encryption
Symantec Endpoint Encryption protects the sensitive information stored across your hard drives and removable media. As a result, there is a lesser risk of data theft and loss.
Features
Below are some of the salient features related to encryption and data security.
- Protects Customers’ Data One of the biggest security requirements of most organizations is to protect customers’ data and privacy to reduce the impact of a potential data breach. Using PGP technology, Symantec ensures that customers’ sensitive data is not exposed to unauthorized users, even in the event of a data breach.
- Compliance An integral part of security is compliance with the local laws and industry regulations such as PCI-DSS, HIPAA, GDPR, and more. Many times, organizations must have a mandatory encryption system in place to protect customers’ data. Further, these organizations have to inform the government and regulatory bodies in the event of a data breach. However, if they have encryption systems in place, these organizations don’t have to disclose a breach, which in turn, can save their reputation and possible fines.
- Strong Cryptographic Standards Symantec uses FIPS 140-2 encryption, an advanced cryptographic algorithm that uses both symmetric and asymmetric techniques to protect sensitive data. This encryption is also mandated by many governments and industry standards.
- Easy to Use Despite being so advanced, Symantec is simple to use from an end user’s standpoint. All that users have to do is just enter the passphrase once and the underlying single sign-on technology validates the user. This eliminates the need to enter the passphrase multiple times for authentication. You can even use smart cards for seamless encryption and decryption processes.
- Multiple Recovery Tools One of the biggest downsides to encryption is the loss of passphrases. But the good news with Symantec is that it allows you to recover your passphrase in multiple ways. You can choose to set up localized questions and answers and use them to recover or you can do so through a web help desk after authenticating your identity.
Why do we recommend it?
Symantec Endpoint Encryption has recently been taken over by Broadcom and the package is in transition at the moment. Broadcom stresses its encryption suite that provides endpoint, email, file, and data exchange encryption and also provides solutions for encryption coordination with external contacts. So, consider the whole suite rather than just endpoint encryption.
Who is it recommended for?
The Symantec encryption suite can help you to centralize and standardize the management of your encryption services, including key generation and storage. This is a useful solution for large organizations that have a considerable spread of locations and applications that need protection.
Pros:
- Takes a forensic level approach to identity, blocking, and documenting threats
- Highly flexible – available on-premise or as a cloud-based service
- Uses SIEM features to ingest information from across the network to identify threats from anywhere
- Includes advanced threat detection tools – ideal for manual investigations
Cons:
- Would like to see more data visualization options
In short, Symantec is highly flexible and scalable and comes with a robust reporting engine for generating reports for external and internal audits. You can buy this product through a partner or distributor. Click here to find someone in your city. There are no downloads or free trials at the time of writing this piece.
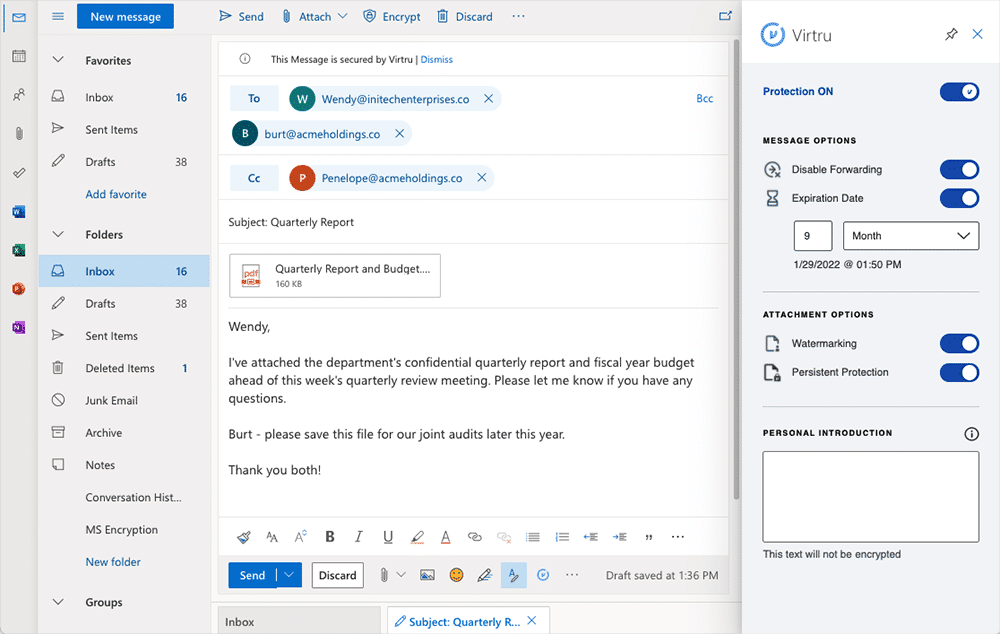
3. Virtru
Virtru is a comprehensive data protection platform that uses encryption to protect your data both at rest and during transit. It also works well with Google Workspace, Microsoft 365, and other SaaS apps and platforms.
Features
Let’s now look at some of Virtru’s features pertaining to data encryption.
- Single, Unified Framework Virtru is a single and unified framework that works well across different frameworks, platforms, and environments. This means you can encrypt your data and keep it safe, even if it travels through custom apps, SaaS, cloud, emails, and more.
- Simple to Use Research shows that most data breaches involve some form of human error. A good way to avoid these errors is to make encryption an intuitive part of a user’s workflow, and that’s exactly what Virtru does. The encryption is automatic for your sensitive data, and users are not expected to do anything. In turn, this automation greatly reduces the errors.
- Secure Data on Google Workspace Virtru works across the entire Google workspace to secure your data across every component such as Docs, Sheets, Gmail, and more. Every file and email stored on the Google Workspace is encrypted, so the chances of a breach reduce greatly. You can even use your encryption keys to keep your private information secure on the Google Cloud Platform.
- Works well with Microsoft Like Google, Virtru also encrypts data on the Microsoft platform. So, all enterprise applications, emails on Outlook, and all files sent and received are encrypted. You can even use the control information to trace contacts, plan resources, and more.
- Compliance Virtru has all the features and reports needed to comply with leading industry specifications such as HIPAA, GDPR, ITAR, CCPA, FERPA, and more. It generates the reports you need for auditing as well.
Why do we recommend it?
Vitru is a data protection platform that provides encryption as part of its data loss prevention strategy. Other features of the package include compliance management for GDPR, CCPA, HIPAA, PCI DSS, SOX, and other data protection standards. The system extends to activity logging, which is another important compliance requirement.
Who is it recommended for?
The important attribute of any company that will attract it to the Virtru platform is that it handles sensitive data. Virtru is open about its pricing, which is rare in the endpoint encryption system field. It has three plans that cater to the three company size bands. All plans start with a five user base price.
Pros:
- Simple management console
- Flexible pricing – affordable for most businesses
- Supports Google Cloud workspace
- Detailed compliance features and options
Cons:
- It can take some time to fully explore all features and options
Overall, Virtru is a handy endpoint encryption tool as it works well not just with your on-prem infrastructure, but also with Google Workspace and Microsoft 365. This way, all sensitive information will be safe regardless of where and how your employees access them.
Virtru offers three pricing plans:
- Starter – $79/month. Ideal for small teams that have to meet compliance requirements.
- Business – $249/month. A good choice for large teams and enterprises that want to secure their data.
- Enterprise – Custom quote. Ideal for large companies that are looking for advanced data security solutions.
Click here to book a demo.
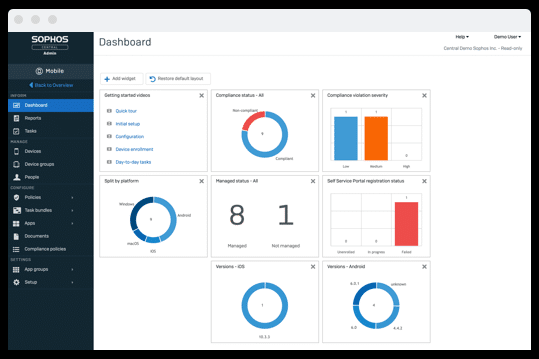
4. Sophos Central Device Encryption
Sophos Central Device Encryption is a full-disk encryption tool that is compatible with both Windows and macOS. It allows you to manage both Windows BitLocker and macOS FileVault encryption systems.
Features
Here’s a look at the features of Sophos Central Device Encryption.
- Full Disk Encryption The highlight of Sophos is its full-disk encryption feature as it protects both your data and the devices that store or use them. Further, it comes with a password-protected HTML wrapper that ensures that only authorized users can access a document or file.
- Simple to Use Sophos Central Device encryption is simple to use and quick to set up. It entails no cumbersome server setups or configurations, so you can start using it within minutes. More importantly, its self-service portal helps to reset passwords and fix other minor issues related to devices. This reduces the workload on IT teams and at the same time, resolves your issues faster.
- Control and Visibility Sophos provides admins with the control and visibility they need to manage devices across the entire infrastructure. You can get all the information you need about disk usage, encryption methods, and other pertinent information needed to understand who has accessed devices, what data was accessed, and more. All this information can be used to reduce the chances of internal threats and at the same time, understand and plug-in vulnerabilities.
- Compliance The work-from-anywhere culture has made it difficult to secure devices and meet the necessary compliance. This is where Sophos can help as it can be installed across devices to encrypt information and the same can be used to increase compliance. Overall, Sophos is a comprehensive tool that encrypts your sensitive data and acts as the first line of defense in the event of an attack.
Why do we recommend it?
Sophos Central Device Encryption focuses on endpoints – it doesn’t manage encryption for peripheral devices. The service interfaces to BitLocker on Windows and FileVault on macOS. Another feature of the tool is that it creates encryption on demand for specific files in order to securely share them with others.
Who is it recommended for?
The benefit of this system is that it enables disk encryption to be managed centrally. A small business that is able to visit each computer individually would probably deploy the FileVault and BitLocker systems directly without the expense of the Sophos service. This package also implements compliance management and Sophos offers a managed version of the tool.
Pros:
- Leverages machine learning and artificial intelligence to stop new and evolving threats
- Offers protection against fileless malware and ransomware
- Users can implement automation to stop threats, or immediately escalate issues
- Scans external devices as soon as they’re plugged into the computer
Cons:
- Better suited for small to medium-sized companies
The pricing structure is simple and is based on your specific needs. Click here to contact the sales team for a custom quote. Click here for a free trial.
5. Check Point Harmony Endpoint
Check Point Harmony Endpoint helps you to centrally enforce encryption on all devices, removable media, and ports. This ensures that your data is not lost or stolen.
Features
Below is a set of important features related to encryption and data security.
- Comprehensive Data Protection Check Point provides comprehensive data protection across your entire infrastructure. Specifically, it encrypts the data stored on removable devices and hard drives, so it is of no use, even if the data is stolen by unauthorized users. It even encrypts data on CDs and DVDs that were burned from endpoint devices.
- Improves Operational Efficiency This tool improves the operational efficiency of your devices as it consumes minimum memory and processing resources. Further, the scan times are quick, which also means optimum resource usage.
- Granular Control Your employees can have granular control over device access settings and usage. You can also customize the configuration settings for removable media and ports. Moreover, all these devices, endpoints, and ports can be managed centrally through a single dashboard. Another advantage is that you can set usage limits for employees based on their job profile and department, and this ensures that no unauthorized user accesses your data. Further, you can track which employee accessed which data, and this can help with tracing as well.
- Logs and Alerts Check Point logs all access information related to devices, endpoints, and ports, so you can refer to them when needed. All this information is stored centrally to help you quickly find what you want. Based on this, you can also set custom alerts for different situations, and these can be sent through multiple channels such as email, SMS, and more.
Why do we recommend it?
Check Point Harmony Endpoint provides anti-malware, threat detection, and disk encryption in a remote monitoring and management package. The system can also block peripheral devices, such as USB sticks from attaching and then let you build up a list of approved devices. The tool will also encrypt USB devices.
Who is it recommended for?
This is a package for use by large businesses with many computers to look after. It can also be extended to a UEM package by adding on mobile device management. The Harmony Endpoint package will replace your existing AV and ransomware protection, so you need to be sure that you are not happy with your current antimalware system before considering this product.
Pros:
- Leverages artificial intelligence to detect and prevent cyberattacks
- Offers bot protection by continuously monitoring the threat landscape
- Provides ransomware detection and phishing protection
- Works well on both smaller networks and enterprise environments
Cons:
- It can take time to fully explore and configure all of the settings available on the platform
In all, this is an advanced tool that encrypts data across all ports and endpoints, and with it, minimizes data theft and loss. Contact the sales team for a custom quote. You can also find a local partner in your city to buy. Click here for a free trial.
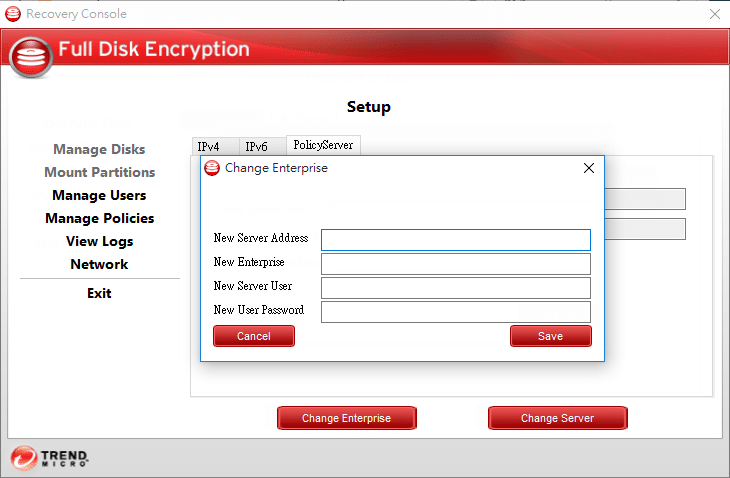
6. Trend Micro Endpoint Encryption
Trend Micro Endpoint Encryption is an advanced tool that encrypts your data across different devices. It also supports enterprise-wide, full-disk, and removable media encryption to keep your data safe and secure at all times.
Features
Read on to know how Trend Micro Endpoint Encryption can protect your data.
- Supports a Wide Range of Devices Trend Micro works well on a wide range of devices, so your employees have the flexibility to install them on any device they use. In particular, it provides extensive visibility into Microsoft BitLocker and Apple’s FileVault – the two most popular tools used for enforcing encryption across devices.
- Streamlines Authentication Trend Micro offers a lot of flexibility when it comes to streamlining authentication and enforcing policies in this regard. It also integrates with Active Directory and supports Multi-factor Authentication (MFA) where required. All this means you can update authentication policies across all devices for uniformity. At the same time, you can configure lockouts and failed password attempts to protect against unauthorized access. Lastly, you can choose to wipe out data remotely on lost and stolen devices.
- Simple to Use A salient feature of this tool is that it is complex enough to provide overarching protection and at the same time, it can be easily managed through a single console. The advantage is that you can centrally manage users and devices and also, simplify access to the existing IT infrastructure.
- Reporting and Auditing This tool enables you to use policy-based encryption to enforce regulatory compliance. It also provides an audit trail that can help with meeting compliance standards. Real-time auditing and unified policy deployment are the other advantages that come with this tool.
Why do we recommend it?
Trend Micro Endpoint Encryption is able to encrypt whole disks or individual files. It can operate on PCs and Macs and it will also encrypt USB devices. This is similar to the Sophos system on our list because it interfaces with BitLocker on PCs and FileVault on Macs.
Who is it recommended for?
Trend Micro is a brand that appeals to small businesses as well as larger organizations. This package includes centralized management, which is a necessary feature for mid-sized and large companies. The encryption service is delivered as part of the Trend Micro Endpoint, Email, and Web Protection package.
Pros:
- Can encrypt virtually all hard drives and removable media
- Centralized management for a simple view of your device security
- Offers advanced reporting capabilities as well as automated audits
- Is FIPS 140-2 certified
Cons:
- Better suited for larger networks
Overall, Trend Micro Endpoint Encryption is a handy tool to streamline access to your IT infrastructure and meet mandatory compliance requirements. Click here for a custom quote. Click here for a free trial.
Thus, these are some of the popular endpoint encryption tools available today. We hope this information comes in handy to decide on the appropriate tool for your needs.
Final Thoughts
To conclude, endpoint encryption tools are those that encrypt data across all devices and ports in your IT infrastructure to ensure that your data is not accessed by unauthorized users. Needless to say, these tools greatly reduce the chances of data loss or theft.
There are many endpoint encryption tools available today and this article has a detailed explanation of five tools that are known for their comprehensiveness, ease of use, and effectiveness.
Feel free to check out our other guides too!
Endpoint Encryption Software FAQs
What are some common features of endpoint encryption software?
Common features of endpoint encryption software include full disk encryption, file and folder encryption, device control, policy management, and remote wipe capabilities.
How does endpoint encryption work?
Endpoint encryption works by encrypting data stored on the endpoint device using cryptographic algorithms that scramble the data in a way that can only be unscrambled with the correct encryption key.
What are some of the benefits of endpoint encryption?
Some benefits of endpoint encryption include improved data security and privacy, compliance with regulatory requirements, and reduced risk of data breaches and data loss.
What are some common use cases for endpoint encryption?
Common use cases for endpoint encryption include protecting confidential data on laptops and mobile devices, securing data on endpoints used by remote workers, and compliance with data protection regulations.
What types of data can be encrypted with endpoint encryption software?
Endpoint encryption software can be used to encrypt a wide range of data types, including files, folders, databases, and entire hard drives.
How does endpoint encryption software protect against insider threats?
Endpoint encryption software can protect against insider threats by preventing unauthorized access to sensitive data stored on endpoints, and by providing audit logs and monitoring tools that can be used to detect and investigate suspicious activity.