Directory services can be a critical component to managing your IT infrastructure. They connect users with the set of services available in a network and give IT admins granular control over who uses what within a network.
A well-known directory service is Active Directory, introduced by Microsoft in 1999 as a part of its Windows Server 2000. This article will take a deep look into what Active Directory is, how it can benefit your organization, and how you can set it up.
What is Active Directory (AD)?
Based on the Lightweight Directory Access Protocol (LDAP), Active Directory takes care of authorizing and authenticating users in your environment to use specific resources or applications.
It also contains extensive information about every user, including their role, personal details, passwords, and their permissions to use different applications.
As you can see, it is a one-stop place to control access and prevent unauthorized use.
But is that all it offers for your organization?
Benefits of Active Directory
Here’s a look at the benefits of AD for your organization.
- Provides simple login access for all global resources
- Enables centralized control and security administration
- Simplifies the identification of specific resources
- Speeds up the process of authorization for resources
- Optimizes productivity
- Helps with capacity planning
- Provides detailed information about hardware and applications, besides better understanding the network
- Simplifies network administration and management
- Efficiently manages trust relationships between domains within an organization
- Improves scalability, especially when there are more organizational units
Types of Active Directory Services
There are seven types of AD services that are deployed across different environments, and they are:
- Active Directory Domain Services (AD DS) Deployed on the server and used for identity
- Azure Directory Federation Services (ADFS) Deployed on the server and used for single sign-on
- Azure Active Directory (AAD) Deployed on the cloud and used for cloud identity
- Azure Active Directory Domain Services (AAD DS) Deployed on the cloud and hybrid environments
- Azure Active Directory Connect Server Provisioning Deployed on the server and used for syncing AD and AAD
- Azure Active Directory Connect Cloud Provisioning Deployed on the server and used for limited syncing of AD and AAD
- Azure Active Directory Application Proxy Deployed on the cloud and used to enable Azure AD legacy apps
Working of Active Directory
AD DS is the main service directory, and it is a part of the Windows operating system. The servers that run this service are called the Domain Controllers (DCs), and often there are multiple DCs, with each containing a copy of the entire domain. These DCs work together, such that a change made to one DC gets updated across all the DCs.
The AD stores users, applications, devices, etc., as objects with a name and attributes. Typically, the AD DS is activated when a user logs into a device or application, and it verifies if the user is authorized to access that object. It also controls which users or groups have access to which resources.
Structure of Active Directory
The Active Directory structure comprises of three components, namely,
- Domains
- Trees
- Forests
Objects like users and devices that use the same AD database are grouped in the same domain. It merits to note that each domain has a DOmain Naming Structure (DNS), and multiple domains can be combined to form another structure called the tree.
These tree structures use a contiguous namespace to ensure that all their domains are arranged logically for easy reference. Also, every domain within a tree has an implicit trust relationship with other co-domains, and there is a secure connection shared among all the domains.
As you may have guessed, a collection of trees is called a forest, where admins can provide specific rights, access, and privileges at all levels of the forest, domain-wide, tree-wide, and forest-wide.
Now that you have a firm idea of what an Active Directory is let’s see how to set it up.
How to Set Up an Active Directory?
As a first step, check if you have the following prerequisites.
- Administrative rights on the server
- A server with a static IP address
- Your Windows server name should match your company’s naming standards
Once you have these, it’s time to start the setup.
Check the IP Address and Admin Privileges
- Open the Server Manager and navigate to the “Local Server” on the left-hand pane
- Scroll down for the static IP address on the right-hand pane and click on it. This opens your network adapter
- Right-click on your adapter and select “Properties”
- Look for IPv4, select it, and click on the “Properties” button
- A window with Ip address will pop up. Check if the preferred DNS address is the same as the IP address
Next, open the PowerShell terminal and double-check if you’re logged in as an administrator.
You must see C:\Users\Administrator at the prompt. Alternatively, run the command “whoami,” and this should return the name of the server/administrator.
Install the Active Directory Domain Services Role
To do this,
- Open Server Manager and look for an option called “Manage” on the top right-hand pane. Click that, and in the drop-down menu, select “Add Roles and Features”.
- This opens a new window, and in it, you’ll see the different things that have to be verified before you can continue under the “Before You Begin” section in the left-hand pane. Run through them all, including the displayed server name to ensure that they are correct.
- Next, run down through the left-hand menu and in “Installation type”, choose if you want a role-based installation or Remote Desktop Services one.
- Moving on, click “Server Selection” on the left-hand pane and choose the server on which you want to set up AD.
- Under “Server Roles”, select Active Directory Domain Services. Sometimes, you may get a pop-up window that asks you to add specific services required for this setup. You don’t have to do much here; just click the “Add Features” button at the bottom. Ensure that the add Management Tools if the required checkbox is clicked as well.
- Next, go back to “Server Roles” and check the “DNS Server” option, and follow the same process as above.
- Finally, navigate to the “Confirmation” option on the left-hand pane and confirm your selection. This will install all the features for you.
Make the Server as a Domain Controller
Once the features are installed, look for a link on the right-hand pane that says “Promote this server to a domain controller” and click it. This opens the Deployment Configuration window, and here’s a step-by-step guide on the selection.
- First off, select the deployment option you want. You can add this domain controller to an existing domain, or you can add it to a new domain in an existing forest, or create a new forest altogether. Next, give the root domain name. Click next, and this will take you to the domain controller option.
- In this example, let’s assume we are creating a new forest to select the functional level. In general, use the maximum available value or the lowest one from the drop-down box. Do the same for the domain functional level as well.
- Next, select the domain controller capabilities and, finally, give a password.
- Moving down, in the “Additional Options” heading, verify the NetBIOS name assigned to the domain and make a change if necessary.
- Next, navigate to “Paths,” where you specify the location of your AD DS database, log files, and SYSVOL folder.
- Finally, review your selection and confirm it.
- The system will run through the prerequisites to ensure that you have everything in place, and if all the prerequisites are present, you can see a green tick box at the top.
After the installation completes, your system will restart automatically. When the system continues, you’ll be prompted for the password you gave earlier. Next, open the Server Manager and click on “Tools” on the right-hand top corner, and in the dropdown menu, you’ll see the management consoles for this Active Directory. Using these consoles, you can manage your AD services.
If you find it overwhelming to manage your AD services, you can always choose third-party tools to manage it.
Here’s a look at some of the popular tools for Active Directory management:
- ManageEngine ADManager Plus – FREE TRIAL A front-end to unify and coordinate multiple AD instances. Runs on Windows Server.
- ManageEngine ADAudit Plus – FREE TRIAL Helps keep your Windows safe and compliant by providing complete control and visibility into the activities in it.
- SolarWinds Access Rights Manager (ARM) A comprehensive tool for managing and auditing access across your entire IT infrastructure.
Let’s take a detailed look at each of these tools.
Our methodology for selecting an Active Directory management tool:
- We’ve assessed tools based on their ability to manage and audit access across IT infrastructures efficiently.
- The capability to validate IT compliance with various standards was a key criterion.
- We prioritized tools that mitigate security risks in real-time and offer robust group management in Active Directory.
- The availability of features like automated user account management and data leak protection was essential.
- We considered the ease of integrating with cloud services like Azure AD as an important factor.
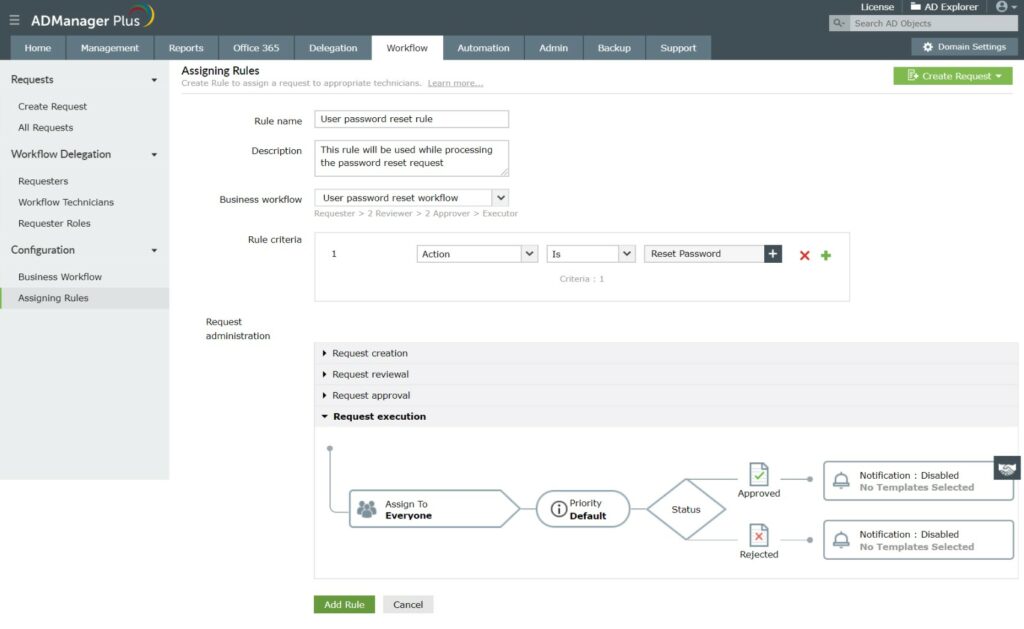
1. ManageEngine ADManager Plus – FREE TRIAL
ManageEngine ADManager Plus enables you to administer all of your Active Directory instances through one console. After you install this software package, you manage user accounts in this dashboard and the system passes those changes on to every AD instance. This enables you to coordinate your user account and device permissions strategy across applications and resources.
Key Features:
- Manages network access rights plus AD for file systems, Microsoft Exchange, Microsoft 365, Google Workspace, and Skype.
- Coordinates accounts and permissions across AD instances
- Import, create, change, and delete user accounts in bulk
- Enforces password policy, such as password rotation rules
- Automatically scans for inactive accounts
- Templates for guided user group management
- Authorization hierarchy
- AD object reports
- Runs on Windows Server
- Cloud option on AWS and Azure Marketplaces
Why do we recommend it?
ManageEngine ADManager Plus is a rival to the SolarWinds Access Rights Manager. The functions of this tool are almost identical to those of the ARM. It covers access rights management for Active Directory, Azure AD, Microsoft 365, on-premises Exchange Server, Skype for Business, and Google Workspace. This software runs on Windows Server.
Who is it recommended for?
System administrators who want to automate their routine AD management tasks should consider this tool. Tasks like bulk account uploads or updates can be handled by this tool and it will also ease the implementation of password security policies and identify abandoned accounts. Assess the tool alongside the SolarWinds ARM.
Pros:
- Facilitates bulk actions
- Tightens password policy enforcement
- Identifies abandoned accounts
Cons:
- No cloud-based version
Pricing: There are three editions of ADManager Plus –
- Free: $0 for 100 domain objects
- Standard: From $595
- Professional: From $795
Download: Start a 30-day free trial.
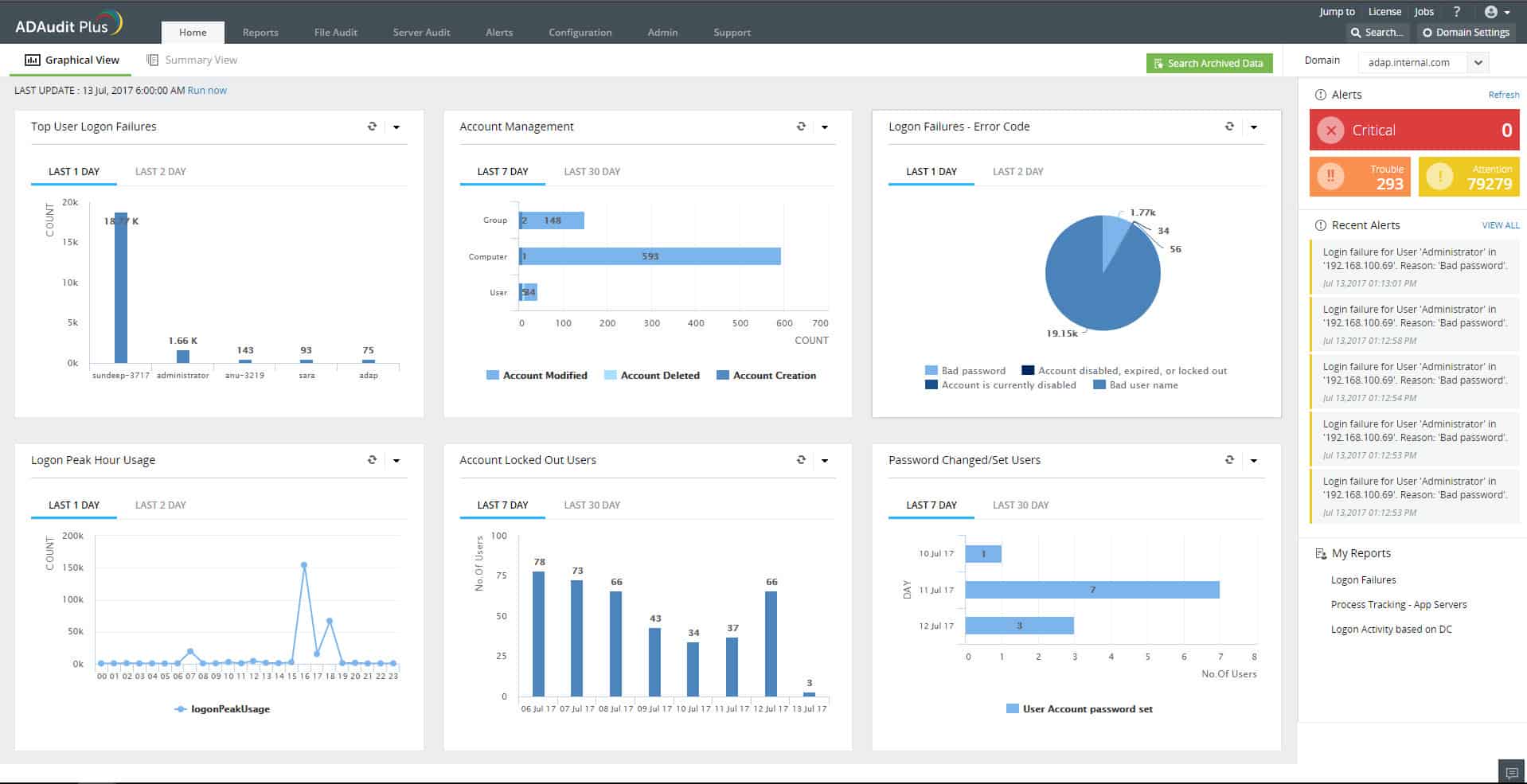
2. ManageEngine ADAudit Plus – FREE TRIAL
ManageEngine ADAudit Plus is a tool that gives comprehensive visibility into the activities that happen in the Windows ecosystem, so you can keep it secure and compliant to industry standards.
Key Features:
- Monitors logins to the different resources on the Windows ecosystem
- Analyzes lockouts to give you complete control over access rights
- Detects changes to users, groups, organizational units, AD objects, and more
- Tracks file accesses and permissions
- Monitors the integrity of Windows workstations
- Sends alerts in real-time
- Generates audit-ready reports
- Detects critical activities and misshapenings
Why do we recommend it?
ManageEngine ADAudit Plus is a specialized tool for user activity tracking. This is a function that you get from the SolarWinds Server & Application Monitor. However, while the SAM tracks all applications, this tool tracks users and their access to resources. This system will also examine any changes made to AD records.
Who is it recommended for?
This is a system security package rather than an Active Directory tool. The system protects AD against tampering by alerting when an entry is changed and enabling those changes to be undone. The main focus of the package is user activity tracking to spot account takeovers and insider threats.
Pros:
- Active Directory security
- Tracks user activity
- Seeks out signs of account takeovers and insider threats
Cons:
- No SaaS option
Pricing: The Standard Edition starts a $595 for 2 Domain Controllers on an annual license, and the Professional Edition Starts at $945.
Download: Start a 30-day free trial.
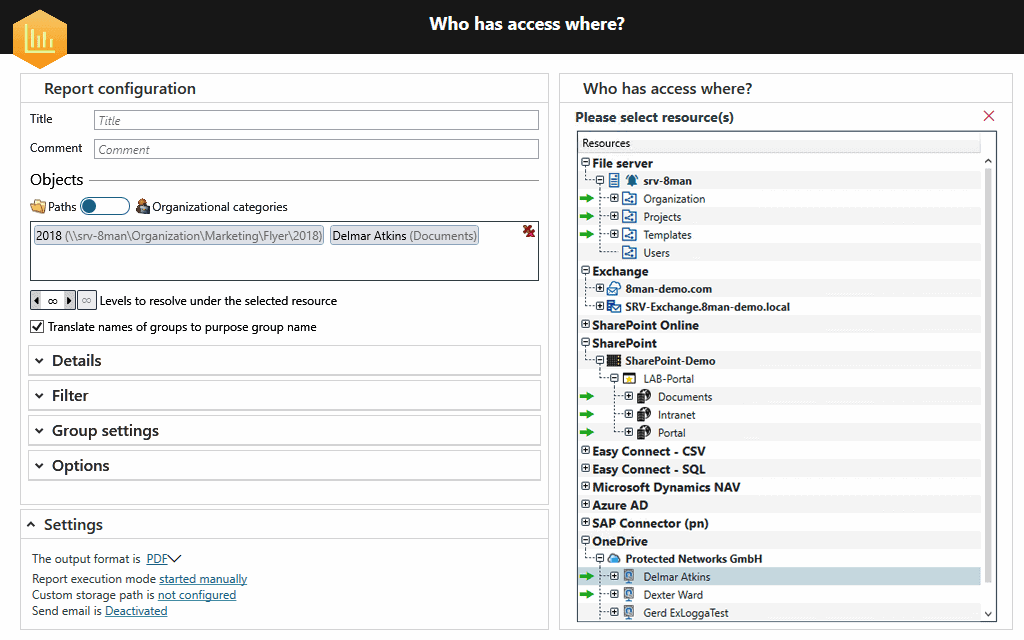
3. SolarWinds Access Rights Manager (ARM)
SolarWinds Access Rights Manager (ARM) is a top-notch tool from SolarWinds that manages and audits access across your entire IT infrastructure through your Active Directory.
Key Features:
- Validates IT compliance for many popular standards
- Mitigates security risks in real-time
- The Active Directory group management tool makes it easy to implement policies and permissions
- Generates permission reports for security and analysis
- Supports SLAs using its provisioning tools
- Automates user account management
- Protects against malicious and accidental data leaks
- Optimizes account management with Azure AD monitoring
- Delegates access rights management
- Understand and acts high-risk access
Why do we recommend it?
Simplify the management of Active Directory with the SolarWinds Access Rights Manager (ARM). Once you install this tool, you will use ARM as your dashboard for AD instead of the native Active Directory utilities. The SolarWinds tool connects to AD and replicates any changes that you make in the ARM dashboard.
Who is it recommended for?
This is a necessary tool for any business that operates multiple domains and that could be because of local access control requirements for systems, such as Microsoft 365 or Google Workspace. You can centralize and coordinate the entries in your domains by attaching multiple domains to your ARM system.
Pros:
- Makes managing AD entries easier
- Updates multiple domains simultaneously
- Operates for application access rights as well as standard AD
- Performs bulk actions
- Compliance reporting
Cons:
- No SaaS version
Pricing: It starts at $1,838
Download: You can test-drive SolarWinds Access Rights Manager (ARM) for a fully functional 30-day free trial.
Conclusion
To conclude, Active Directory is a directory that monitors users, resources, and interactions among these groups. Since this centralizes management and administration and gives fine control over access privileges, it is popularly used in Windows environments the world over today.
Such a comprehensive tool has a multi-step process for enabling and setting it up on Windows servers, and following the above steps can help you get it going within just a few minutes. Besides setup, you also have to monitor it regularly, and for this, there are many third-party tools.
The above three tools mentioned in this article are well-known and comprehensive in their monitoring, and they can come in handy to manage your Active Directory environment with relative ease. However, while you can pick any of the three tools, consider the size and complexity of your environment, the ancillary services you may need, the associated integrations, and your budgetary constraints before choosing the appropriate one.
Active Directory Setup FAQs
What are the prerequisites for setting up Active Directory?
Prerequisites for setting up Active Directory include having a Windows Server environment, an appropriate DNS infrastructure, and a valid domain name.
How do you install Active Directory on a Windows Server?
To install Active Directory on a Windows Server, you need to use the Server Manager tool and follow the steps in the Active Directory Domain Services (AD DS) Installation Wizard.
What are some common issues that can occur during Active Directory setup?
Common issues that can occur during Active Directory setup include DNS configuration errors, issues with domain name registration, and problems with domain controller replication.
How can you monitor the health and performance of Active Directory?
You can monitor the health and performance of Active Directory by using monitoring tools such as Windows Performance Monitor, Active Directory Replication Status Tool, and Active Directory Domain Services Performance Counters.
How do you manage Active Directory users and groups?
You can manage Active Directory users and groups using the Active Directory Users and Computers (ADUC) tool, which allows you to create, modify, and delete user and group accounts, and assign permissions and access rights.
How do you configure Active Directory security?
Active Directory security can be configured by defining security policies, permissions, and access controls for users and groups, and by using tools such as Group Policy Management Console (GPMC) to configure security settings across the network.
What are some common Active Directory-related attacks?
Common Active Directory-related attacks include password attacks, privilege escalation attacks, and domain controller compromise attacks.
How can you secure Active Directory against attacks?
You can secure Active Directory against attacks by implementing appropriate security policies and access controls, using strong authentication mechanisms such as multi-factor authentication, and regularly monitoring and auditing Active Directory activity for signs of suspicious or unauthorized activity.