You’ve decided you want to get a better handle on your network. Maybe you’re looking at setting up some monitoring. But then you discover you need to configure this thing called SNMP, and that’s when the problems start. There are things to configure that you’ve never heard of: OIDs, MIBs, traps, informs, polling, and versions. What the heck is all this stuff anyway, and do you need to know it all?
In this first part of a series on SNMP you’ll learn the basics, and see how it can help you make your network more reliable and easier to manage.
What the Heck is SNMP Anyway?
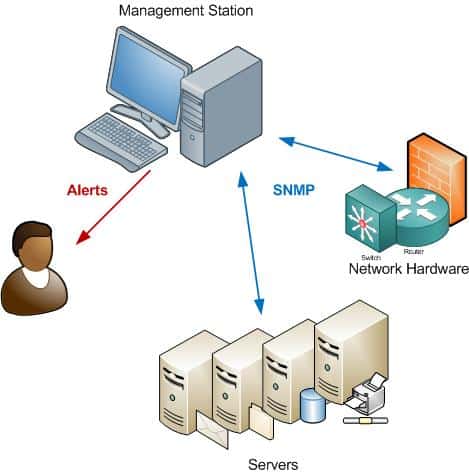
SNMP stands for Simple Network Management Protocol. It is a standard way of monitoring hardware and software from nearly any manufacturer, from Juniper, to Cisco, to Microsoft, Unix, and everything in between. SNMP requires only a couple of basic components to work: a management station, and an agent.
First, a management station is required. The management station is simply software that collects information from your network. Most management stations will poll your network for information at regular intervals, as specified in the configuration. This collected information is compared against the baseline values for each metric to understand underlying issues.
When you use an advanced monitoring tool like ManageEngine OpManager, it also sends context-rich alerts when the current values are outside the range of established thresholds. Using this information, network administrators can identify the root cause of the problem and troubleshoot it.
Another advantage of selecting a tool like OpManager is its visualization capabilities. It can generate extensive reports for further auditing and compliance, and also represent the data across charts and graphs for a better understanding. Due to these features, OpManager is a go-to tool for SNMP monitoring. Download a 30-day free trial.
Second, the hardware or software that you want to monitor must have an agent running. The agent collects information, and then sends it to the monitoring station when polled. Agents can also send notification to the management station without being polled, for example if an error is detected.
Agents are usually built-in to your network hardware and software – they simply need to be enabled and configured.
What Can It Do?
SNMP is very simple, yet powerful. It has the ability to help you manage your network by:
- Provide Read/Write abilities – for example you could use it to reset passwords remotely, or re-configure IP addresses.
- Collect information on how much bandwidth is being used.
- Collect error reports into a log, useful for troubleshooting and identifying trends.
- Email an alert when your server is low on disk space.
- Monitor your servers’ CPU and Memory use, alert when thresholds are exceeded.
- Page or send an SMS text-message when a device fails.
- Can perform active polling, i.e. Monitoring station asks devices for status every few minutes.
- Passive SNMP – devices can send alerts to a monitoring station on error conditions.
Versions and Security (or Lack Thereof)
Several versions of SNMP are supported, v1, v2c, and v3. Nearly all monitoring stations support all three versions. So why not simply use the newest version all the time?
Version 1 is the simplest and most basic of the versions, and there may be times where it’s required to support older hardware. But version 2c adds several enhancements to the protocol, such as support for “Informs”. Because of this v2c has become most widely used.
However, a major weakness of v1 and v2c is security. Community strings – the equivalent of passwords – are transmitted in clear text and there is no support for authentication. This creates risk that your community strings could become compromised. This is not good, especially considering the power SNMP has to change device configuration.
SNMP v3 adds a security features that overcome the weaknesses in v1 and v2c, and it should generally be used if possible – especially if you plan to transmit information across unsecured links. However, the extra security makes it much more complex to configure.
Ports and Firewalls
SNMP uses UDP as the transport protocol. If management traffic will traverse firewalls, make sure that the following default ports are open:
- UDP 161: Used when management stations communicate with agents, e.g. Polling
- UDP 162: Used when agents send unsolicited Traps to the management station
MIBs, OIDs and Traps, Oh My!
The basics of SNMP are simple, but terminology is one of the needlessly complicated parts of SNMP. However, it’s easily understood. In the next article we’ll help clear the confusion around things like “strings”, and “MIBs”.
After that, we’ll look at a few tools you can use to explore SNMP in greater detail, and start using it to automate critical monitoring tasks. In the meantime, check out our Downloads page for links and reviews of many popular monitoring systems and tools.
SNMP Basics FAQs
What are some common uses of SNMP?
SNMP is commonly used for network monitoring, device management, and performance analysis.
What types of network devices can be managed using SNMP?
SNMP can be used to manage various types of network devices, including routers, switches, servers, and printers.
How does SNMP work?
SNMP works by using a network management system (NMS) to send requests to network devices, which then respond with information about their configuration, status, and performance.
What are SNMP agents?
SNMP agents are software components that run on network devices and respond to SNMP requests from the NMS.
What are some common SNMP monitoring tools?
Common SNMP monitoring tools include Nagios, Zabbix, Cacti, and PRTG.
What are some best practices for using SNMP?
Best practices for using SNMP include securing SNMP communications using SNMPv3, configuring SNMP community strings to limit access to network devices, and using SNMP monitoring tools to analyze network performance.
What types of security risks are associated with SNMP?
SNMP can pose security risks if used improperly, such as exposing sensitive information or allowing unauthorized access to network devices. It is important to follow best practices for securing SNMP communications.
How can SNMP be used in cloud-based environments?
SNMP can be used in cloud-based environments, including public, private, and hybrid cloud environments.
What types of compliance certifications does SNMP have?
SNMP does not have specific compliance certifications, although it is commonly used in compliance frameworks such as HIPAA and PCI DSS for network monitoring and management.