This is part 2 of our SNMP basics tutorial.
Terminology is one of the needlessly complicated parts of SNMP. But don’t fear, it’s really very simple once understood. This page will help you understand basic SNMP terminology. We’ll start with the more important concepts in the next few sections, and a glossary of other terms can be found at the bottom of this page.
OIDs and MIBs
Two crucial SNMP concepts are OIDs (Object Identifier) and MIBs (Management Information Base).
SNMP works by querying “Objects”. An object is simply something that we can gather information about on a network device. For instance, an object might be something like Interface Status. Querying Interface Status would return a variable – the interface could be Up, or Down. SNMP identifies objects like with an Object Identifier, or OID.
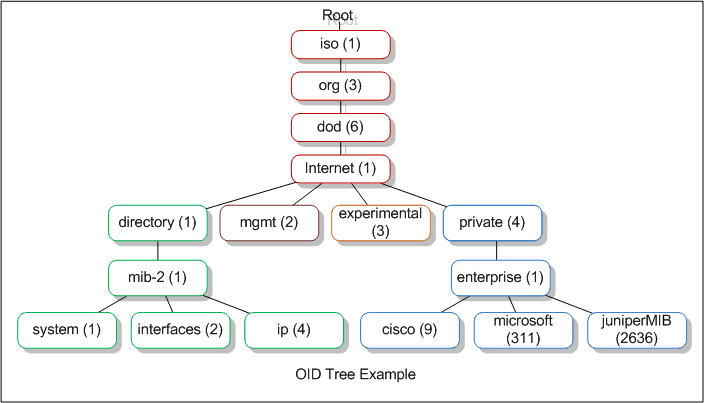
Most network management software has the ability to display the OID tree in some way. For example in the screenshot below, the OID tree is displayed in a folder-style list:
Closely related to the concept of an OID, are MIBs. A MIB is like a translator that helps a Management Station to understand SNMP responses obtained from your network devices. All SNMP devices generally support something called MIB-2, which is a standard set of objects that can be monitored. The Interface status object mentioned earlier is part of this group, as are most system objects like CPU or memory utilization.
Just to complicate things a little further, manufacturers can supply custom MIB files for their hardware. As an example, some hardware supports environmental monitoring of temperature or fan speeds. These objects aren’t found in the standard MIB-2 group, so manufacturers supply custom MIB files to add support for these features. The custom MIB files are loaded in to your NMS to tell the software which SNMP objects can be queried, and how to display the results.
Manufacturers register their custom objects under a different part of the OID tree from MIB-2. In the OID tree graphic above, you can find manufacturer’s objects in the blue section, under “Enterprise.” So, Microsoft would be 1.3.6.1.4.1.311 in the hierarchy, and Juniper is 1.3.6.1.4.1.2636.
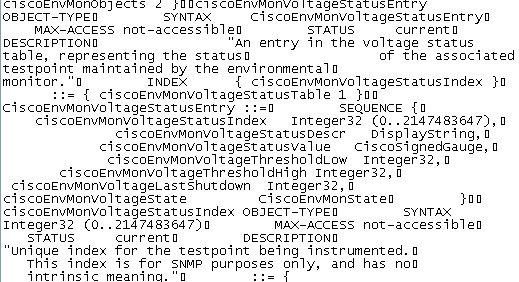
MIB files themselves are difficult to read, they are only meant to be imported, or “compiled” by a Management Station. Below is an example of a Cisco MIB file for environmental monitoring.
Cisco provides a useful resource for looking up OID values, and downloading MIB files for any of their devices. You can access it here.
Community Strings
Community strings are another important SNMP concept. Community Strings are like passwords. They are used to allow authorized users to access the SNMP agent on a device. Unfortunately, many admins never change community strings from the defaults “Public” for read-only, and “Private” for read-write.
Community Strings can be configured as read-only(RO), or read-write(RW). As the name implies, read-only strings only allow information to be pulled from the agent. However, read-write strings are much more powerful, and can allow re-configuration of many of a device’s properties. Use extreme caution when implementing read-write strings. Earlier versions of SNMP transmit strings in clear-text, raising another security risk. See versions below.
More Terminology
Some general SNMP terminology that you may come across:
• Agent: A process that monitors devices for problems and sends alerts to a monitoring station.
• Community Strings: Like passwords. See earlier in this article for more information.
• Get: SNMP sends a get request to device it monitors to retrieve specific information.
• Get Next: A getnext command is used by SNMP to get the next variable in a set – for instance in a table.
• Informs: Like Traps, but sent by the agent with a request for the management station to confirm receipt. Supported in v2 and up.
• Management Station (aka Network Management Station or NMS): The software configured to receive and collect information sent from SNMP agents.
• MIB: Management Information Base. See the beginning of this article for more information on MIBs.
• MIB Browser (or MIB Walker): A tool that can pull data from SNMP enabled devices, helping to identify which objects respond to a query.
• Notification: Same as a “Trap”. V2c and up use the term Notifications to refer to a Trap.
• OID: Object Identifier. See the beginning of this article for more information on OIDs.
• Object: The things SNMP gathers information about. Examples are Interface status, or CPU utilization.
• Polling: An NMS will poll, or ask devices for their status regularly.
• Set: SNMP can use a Set command to change settings on a device.
• Trap: SNMP sends a trap, or unsolicited message sent from an agent to a management station when some important event is detected. This is the opposite of polling.
• Variable: Variables are the actual status of an object – up/down, 90% CPU used, etc.
• Version 1: Original version of SNMP, community strings sent in plain text, very weak security.
• Version 2c: SNMP v2c was developed to fix some of the problems in v1. However multiple versions were developed, none truly addressing the problems with v1. V2c is the most common flavour, and has enhanced protocol handling over v1, resulting in slightly improved operations. However, security is still an issue because it uses plain-text community strings.
• Version 3: The newest version of SNMP, v3 supports full security and authentication. Should be used if possible, especially on untrusted networks.
In our next article we’ll look at some practical ways you can use SNMP tools to make your job a little easier.
SNMP Tutorial FAQs
What are the components of SNMP?
The components of SNMP include management stations, agents, and the Management Information Base (MIB).
What is the role of a management station in SNMP?
The management station is the computer or software application used to manage network devices using SNMP.
What is the role of an agent in SNMP?
The agent is software installed on network devices that collects and reports information to the management station.
What is the Management Information Base (MIB)?
The MIB is a database that contains information about the network devices being managed using SNMP.
What are SNMP traps?
SNMP traps are notifications sent from network devices to the management station when specific events occur, such as a device failure or a change in network configuration.
What are SNMP communities?
SNMP communities are groups of network devices that share a common authentication and authorization mechanism.
What are the versions of SNMP?
The current versions of SNMP are SNMPv1, SNMPv2c, and SNMPv3.
What is the difference between SNMPv1, SNMPv2c, and SNMPv3?
SNMPv1 and SNMPv2c are older versions of SNMP that provide limited security features, while SNMPv3 provides stronger security features such as encryption and authentication.
What types of information can be monitored using SNMP?
Information that can be monitored using SNMP includes network traffic, device uptime, CPU and memory usage, and device configuration settings.
What are some common SNMP monitoring tools?
Common SNMP monitoring tools include SolarWinds Network Performance Monitor, PRTG Network Monitor, and Nagios.
How can SNMP be used for network performance monitoring?
SNMP can be used for network performance monitoring by collecting data from network devices and generating alerts based on predefined thresholds.
How can SNMP be used for network configuration management?
SNMP can be used for network configuration management by collecting and storing device configuration settings in the MIB.