An attack known as a USB attack does what it says: it makes use of a USB-connected device, such as a thumb drive or hard drive, to install malicious software on a computer or another USB-connected device, such as a smartphone. Other examples of USB-connected devices include thumb drives and hard drives. The delivery of an electrical charge is another method through which malicious USB devices can be utilized to damage or destroy a computer.
This article will guide you through all the threats that are given by an unsecured USB terminus and provide various methods that you can utilize to increase your defense against those dangers.
What are some ways that you can ensure the safety of your USBs?
Protecting your USB flash drives is the easiest course of action to take given that they are the source of the virus that is spreading. This form of danger, on the other hand, does not have to originate from a USB flash drive; it can arise from any location inside your network. For example, one of your computers might accidentally pick up a virus that replicates itself and infects your USB flash drives.
This means that to be safe, you need to handle the issue from both an external and an internal perspective. On the external level, you need to protect the USBs that your firm uses, and on the inside level, you need to safeguard any devices that could connect to USB flash drives.
How do USB devices become contaminated with malicious software?
Both incidental and purposeful transmission of illness is not impossible to come across. This latter scenario is shown by the Stuxnet worm; in this scenario, someone installs malicious code onto the drive to filter the code into the network that is being attacked.
An unintentional infection could take place if a person in a public area like an internet café, an airport, or any other location with inadequate endpoint protection inserts an unprotected USB drive into a system with inadequate security (which is about 70 percent of places). The infection may become apparent at some point after you have connected the device to your computer; however, there is no way to know for sure how much damage has already been caused.
Step by Step Guide on how to Protect your USB Firmware from Viruses
Step 1: Steer clear of unidentified USB devices
This method involved leaving deliberately infected USB sticks out in public. People with a sense of adventure would pick up these flash drives, bring them to their place of employment or school, and plug them in, which would cause the network to get infected with the malicious content that was loaded on the firmware.
Because more people are aware of the risks associated with connecting unauthorized USB devices, this problem has significantly decreased in frequency over the past few years. Despite this, it is still something to think about, particularly in light of the recent surge of USB-centric gadgets that have dominated the market.
This concept is most commonly used with USB flash drives; however, in theory, it can be implemented with any device that connects to a computer through a USB connection. Therefore, be wary of any peripheral that you are unfamiliar with, and if you are the administrator of a network, make it a point to warn and educate your users about the risks associated with plugging random gadgets into their USB ports.
Step 2: Turn off auto-play mode
One of the most significant vulnerabilities that might impair the physical security of a network is Windows Auto-play, which automatically starts programs when they are opened. But in most cases, all it does is spare the user the five seconds that are required to manually start a linked device.
Windows Auto-play is a feature that can be used by malicious USB firmware to run programs that can completely disable your network. It is preferable to stop this Windows feature across your network as a real catch-all for the majority of USB firmware-based malware. Even if more advanced malware can typically find a way to circumvent it in some way, it is still best to do so.
Step 3: Do not connect to any unidentified drives
A significant portion of dangers posed by USB devices are the result of social engineering, which refers to the use of psychological deception and manipulation to get users to connect to a malicious device. You mustn’t fall for this tactic, as it is utilized in virtually every variety of online attack.
If you find a USB drive that you aren’t familiar with dropped somewhere, such as a parking lot, you should not attach it to your computer at any time. Negative actors count on human curiosity to assist them in infecting your device so they can steal your information. They will leave it in a public place, such as a hospital, and watch for someone to connect it to an outlet there. This type of attack is known as a drop attack.
Sending USB drives to individuals through the mail while making them appear to be promotional offers from large-format technology retailers like Best Buy is another popular strategy. In a nutshell, you should be suspicious of any free USB sticks that you come across or receive unexpectedly, regardless of whether they come from a company that you are familiar with or not.
Step 4: Go virtual
Virtualization software, such as Oracle’s free VirtualBox, can be downloaded if you have a higher level of technical expertise (Opens in a new window). It gives you the ability to construct a virtual environment on your computer, which will then run a simulated instance of your computer within your computer. You can plug in the drive, and then open it in the virtual environment, and neither your files nor your network will be affected in any way. Users of Windows have access to an additional built-in option called Windows Sandbox.
Step 5: Updates should not be ignored
Make sure that your operating system is always up to date, especially if you are using Windows. A large number of cybercriminals capitalize on the fact that users frequently put off updating their systems, even though these updates frequently address critical flaws.
Step 6: Use USB flash drives that are safe
On the market, you can choose from a few different USB flash drives that have been constructed safely. If, on the other hand, you find yourself utilizing a single personal flash drive regularly, perhaps because it holds portable software for use in network administration, then you may want to think about updating.
One such approach is to use an encrypted flash drive, such as the ones that are manufactured by Ironkey. You can avoid both human and automated infection of the USB’s firmware by encrypting access to the flash device. Additionally, you can be certain that the core firmware on such a drive was developed with security in mind, making it more resistant to the malicious changes that can be caused by viruses. This gives you an added layer of peace of mind.
Another type of hardware-based USB protection is seen in flash devices with a keypad, such as the Kingston Datatraveler 2000. This approach eliminates any risk of software infection because it requires a password to be physically input. For an infection to occur, an attacker would need to know your passcode in addition to having physical access to your USB flash drive. In addition, the majority of keypad flash drives also come equipped with encryption software, enabling you to increase the level of protection for your data.
Certain USB Flash Drives come with a write protection feature, which is commonly implemented as a little latch on the side of the flash drive. The USB drive’s ability to report information to or receive information from a connected device is disabled when the write protection switch is turned on. You are then able to look at the contents of the drive without worrying about your device becoming infected. In addition, the fact that the write protection latches are physical means that they are capable of preventing all software-based infections, very similar to how a keypad solution works.
Step 7: Disable autorun
When you plug in a drive, it will help prevent harmful code from automatically running on your device, which is provided by features on your devices. Open the Control Panel on your Windows computer, then look for the AutoPlay setting there. Uncheck Employ the AutoPlay function on all of your media and devices to stop unknown devices from starting up without first notifying you or requesting permission from you.
Step 8: Software for controlling devices
Device control software is without a doubt one of the most effective solutions that you can implement across your network. This software keeps track of and manages any data that is exchanged between the devices on your network and any portable storage, such as USB flash drives, in any way. It should come as no surprise that data loss prevention (DLP) software and device control software work hand in hand. You’ll find that several solutions for device management are included in comprehensive DLP software packages.
You can use device control software to physically stop any unauthorized USB devices from connecting to your network by providing a centralized point of control for all external device connections. This allows you to block any unauthorized USB devices from connecting to your network. Alternately, if you continue to let connections from flash drives, you have the option of monitoring the files that are being sent and marking those that might be malicious.
There is a vast selection of software for controlling devices available on the market today. Below, you’ll find our analysis of various potential solutions to this problem.
Tools to Help you Protect your USB Firmware
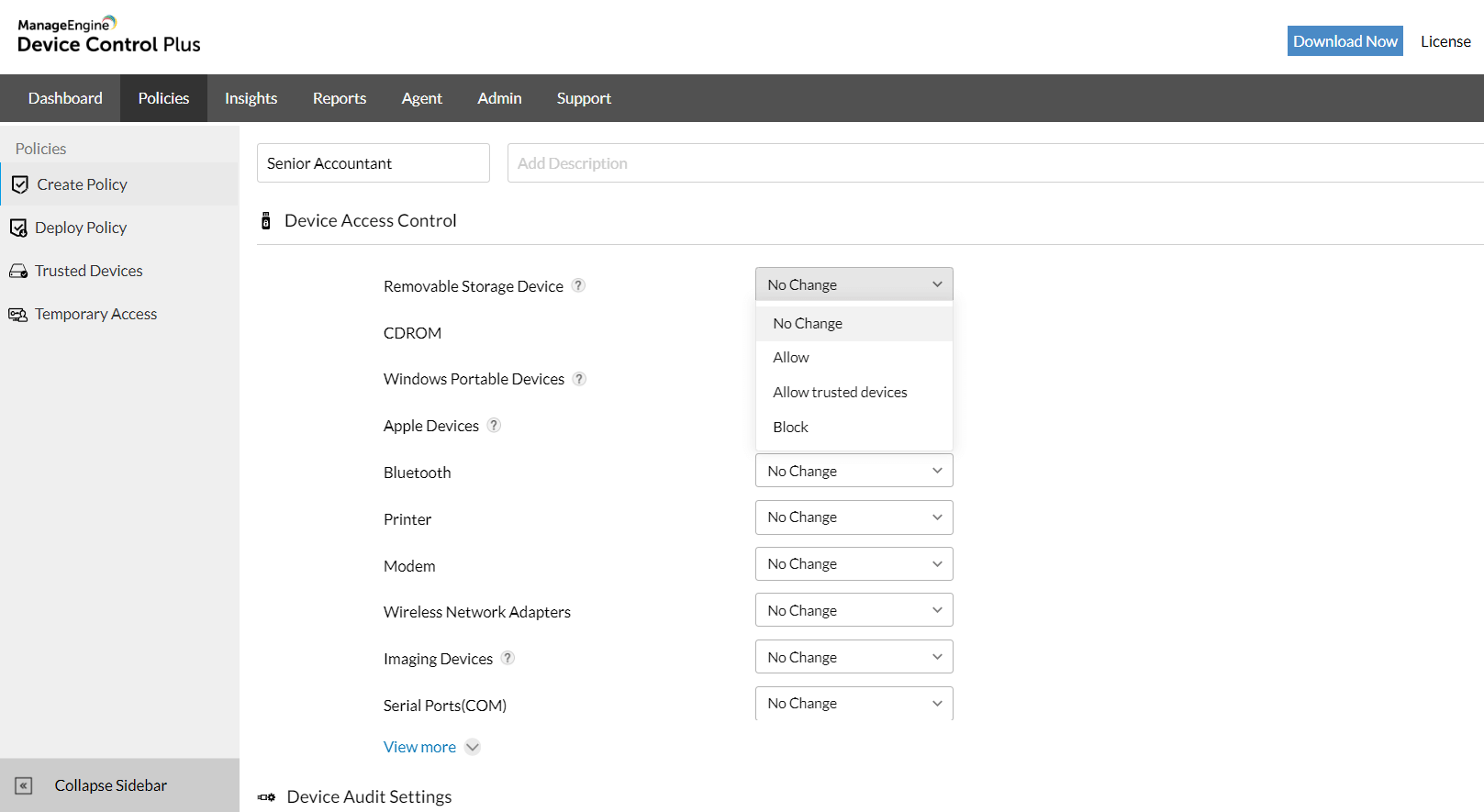
1. ManageEngine Device Control Plus – FREE TRIAL
ManageEngine Device Control Plus locks down USB ports and then the administrator sets up an allowlist. That list can be nuanced, allowing different levels of access rights. The tool can also be set to block software from copying onto a computer from a USB devices. This prevents malware from getting off your USB to your computer. Preventing malware from getting off your computer onto a USB device is a much bigger task and it is expected that your computer is malware-free thanks to third-party antivirus systems. This package runs on Windows Server and you can get it on a 30-day free trial.
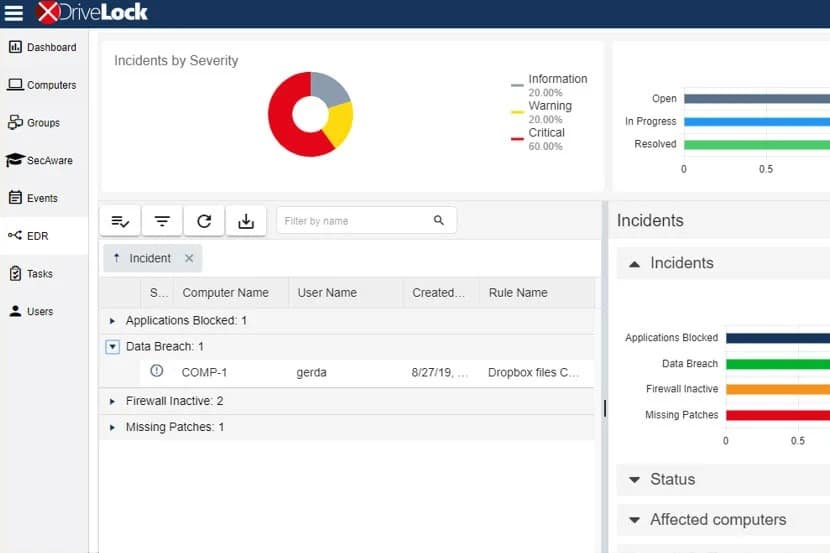
2. Drivelock
If you use the Drivelock USB restrictions in conjunction with the accompanying encryption and antivirus system, you may entirely protect a device from being infected by malware that spreads through USB drives. In addition, this software gives you the ability to define security limits based on any removable storage medium, not simply USB flash drives as was previously possible.
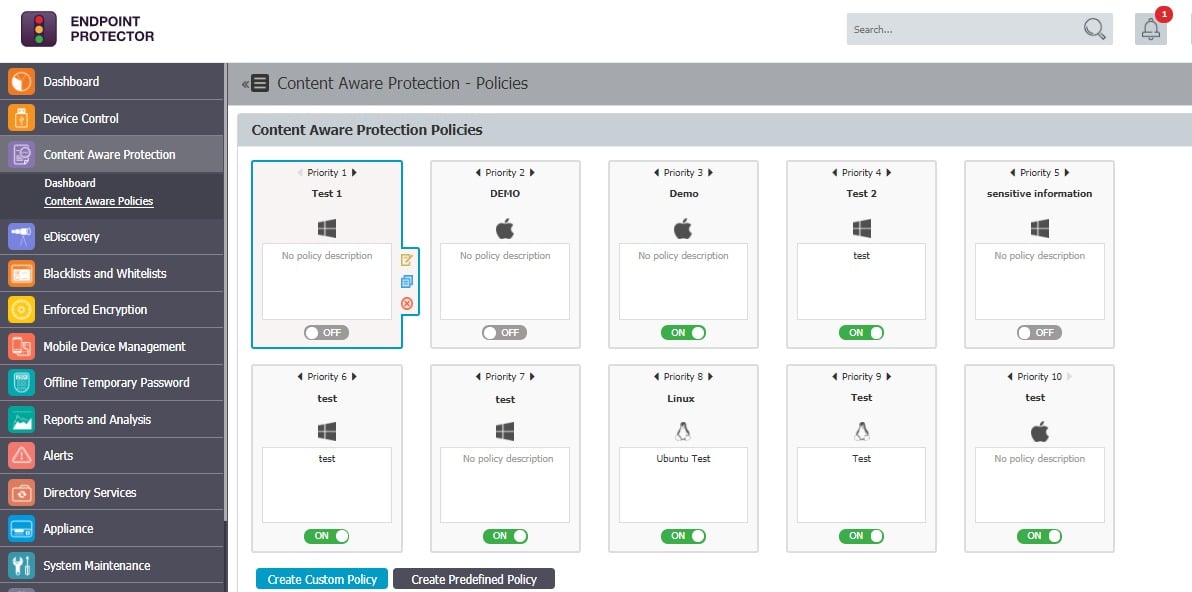
3. Endpoint Protector by CoSoSys
Endpoint Protector protects your network from nefarious assaults that are based on USB firmware by having a built-in Device Control capability. You can monitor your network through the use of a web-based interface if you provide a lightweight agent that is deployed on all of your devices.
Conclusion
We’ve gone through a few different approaches that you may take to protect your USB flash drives and network in this article. You should at the very least educate your users on the dangers of connecting unknown USB devices, and you should also consider deactivating Autoplay via group policy.
If you want to increase your security even further, you have several other options available to you, such as enhanced USB flash drive hardware security. You should also take into consideration one of the many accessible device control software options, such as Device Control Plus or Endpoint Protector by CoSoSys. Both of these programs are excellent choices.
Protecting your USB Firmware FAQs
How can I protect my USB firmware from viruses?
You can protect your USB firmware from viruses by following best practices such as scanning your USB device with antivirus software before using it, avoiding using untrusted USB devices, using a read-only mode on your USB device if possible, and updating your USB device firmware regularly.
What should I do if my USB firmware gets infected with a virus?
If your USB firmware gets infected with a virus, you should disconnect the device from your computer immediately and scan your system with antivirus software. You may also need to reformat your USB device and reinstall the firmware to ensure that it is clean and secure.
Are there any tools or software programs that can help protect USB firmware from viruses?
Yes, there are various antivirus software programs that can scan and protect USB firmware from viruses, such as Norton, McAfee, and Bitdefender. Additionally, some USB devices come with built-in security features, such as encryption and password protection, which can help protect your data and firmware from unauthorized access.
Can USB firmware be updated?
Yes, USB firmware can be updated by downloading the latest firmware update from the manufacturer's website and following the instructions provided in the firmware update package.
What are some signs that my USB firmware may be compromised?
Signs that your USB firmware may be compromised include slow performance, unusual errors or messages, unexpected file names or extensions, and unauthorized access to your device or data.
What should I do if I suspect that my USB firmware has been compromised?
If you suspect that your USB firmware has been compromised, you should disconnect the device from your computer immediately, run an antivirus scan on your system, and contact the device manufacturer or a professional security expert for further guidance and assistance.
Can USB firmware viruses infect my computer?
Yes, USB firmware viruses can infect your computer if the infected USB device is plugged into your computer. Once the infected firmware is installed on your computer, the virus can spread to other devices or compromise your system.
How can I prevent USB firmware viruses from infecting my computer?
To prevent USB firmware viruses from infecting your computer, you should use antivirus software and keep it up to date, avoid using untrusted or unknown USB devices, disable autorun and autoplay features, and regularly scan your system for malware and viruses.