As an end-to-end SIEM solution SolarWinds Log & Event Manager (LEM) aggregates, correlates and normalizes log and event data, and stores them in one single repository for centralized management. LEM extends it functionality to allow quick and easy search of the stored event data. Let’s understand the power of this advanced, intuitive IT search that helps IT pros quickly scan through and search for historical event data and get them on a report for analysis and forensics.
nDepth is a powerful search engine within the LEM console that lets you search all of the alert data or the original log messages that pass through a particular Manager. The log data is stored in real time, as it originally occurs from each host (network device) and source (application or tool) that is monitored by the Manager. You can use nDepth to conduct custom searches, investigate your search results with a graphical tools, investigate alert data in other explorers, and take action on your findings.
LEM has two data storage areas – one to store the messages from the original event logs, and one to store the normalized alert data that the Console reports in the Monitor view.
- In Alerts mode, nDepth summarizes and explores your alert data. This is the normalized data that appears in the Monitor view and is stored in the LEM database.
- In Log Messages mode, nDepth summarizes and explores the raw log messages that are going into nDepth Log Storage from the original event logs. This mode is intended for security admins who have specific data analysis needs, and who fully understand how to interpret the raw log messages that are generated by their network devices and tools.
Both, the raw log messages, as well as the normalized data, are viewed within the same LEM console.
nDepth summarizes and displays search results with several different visual tools that can also be combined into a customizable dashboard. The tools are intuitive and interactive – you can point and click to refine your searches. Each graphical tool provides an alternative view of the same data, so you can examine your data from several perspectives. You can also view and explore a text-based view of the actual data.
These visual anlytical tools are:
- Word Clouds: This shows keyword phrases that appear in your alert data. Phrases appear in a size and color that relates to their frequency. You can filter this view to zero in on a range of activity. You can also click a phrase to create or append a search based on that phrase. Word Clouds is the first-of-its-kind implementation in a log monitoring system.
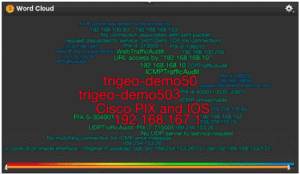
Word Cloud Visualization
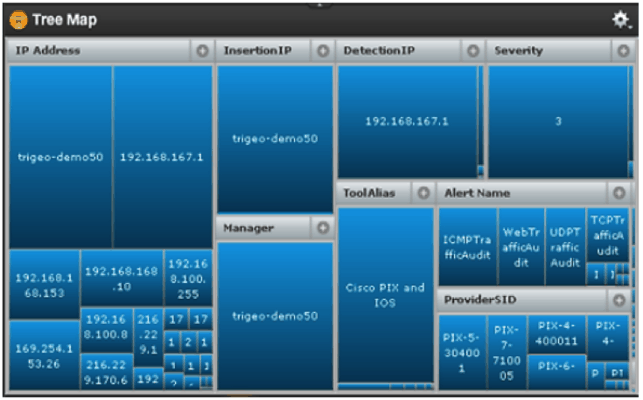
- Tree Map: This shows the items that appear most often in the data as a series of categorized boxes. The size of a box within each category is associated with its relative frequency. The more often an item occurs, the larger its box appears.

Tree Map
- Bar, Line, Pie Charts: These are a group of widgets tha shows your most frequent data items as a series of bar, line and pie charts.
- Bubble Charts: This shows your most frequent data items as a series of circles or “bubbles.” The size of each bubble corresponds with the item’s relative frequency. The more often an item occurs, the larger its bubble appears.
Using the nDepth Widget Builder, you can create a new nDepth widget or edit the configuration of an existing nDepth widget.
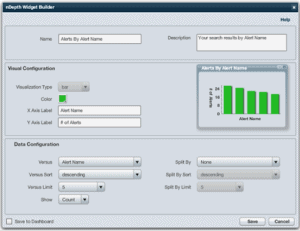
nDepth Widget Builder
- Histogram: nDepth’s histogram summarizes alert activity within a particular period. This histogram is for a search of the last 10 minutes of alert activity. The bright zone shows the period that is currently being reported. The gray zones show activity outside of the reported period.
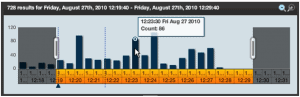
Histogram
Result Details is a text-based view of all of the data you are investigating. This feature also supports nDepth’s search capabilities allowing you to create or refine searches by dragging and dropping search strings from the search data into nDepth’s search box.
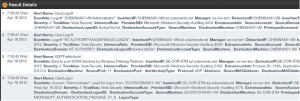
Result Details
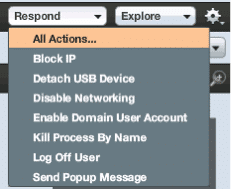
Based on the resuslt details of the search, you can use the “Respond” button to perform responsive actions like Block IP, Detach USB Drive, Logoff User, etc.
Export Search Data into Ad Hoc Report: Search data can easily be converted into ad hoc reports which can later be exported as PDF. The title of the report, graphs, and pages can be customized as desired.
LEM simplifies the search process by allowing you to save the search already carried out. These searches can be saved and later run again as required.
Export Data into ad-hoc report
To consolidate, the nDepth feature in SolarWinds LEM can be used to:
- Search normalized alert data and the original log messages, and can also be used to explore log messages that are stored on a separate nDepth appliance.
- Intuitively view, explore, and search significant alert activity. nDepth summarizes alert activity with simple visual tools that you can use to easily select and investigate areas of interest.
- Conduct custom searches with the Search Builder
- Save and reuse custom searches
- Export your findings to a printable report in PDF format, or your search results to a spreadsheet file in CSV format.
- Use the Respond menu to take action on any of your findings.
- Export your findings to a report in PDF format.
With a wide variety of other features like real-time event correlation, 300+ pre-build audit-proven compliance reports ready for use, Active Response technology to respond immediately to network threats, LEM is just the SIEM solution that can keep your infrastructure secure while saving a ton of time, effort and post-disaster hassle!
Download a Free Fully-Functioning 30-Day Trail of Log & Event Manager