Many of us know Wireshark as a free and powerful protocol analyzer, allowing us to capture and analyze traffic when we need to and where we need to. Wireshark is great in the way of flexibility especially with its recent v2.0 release.
- Newly reformed UI
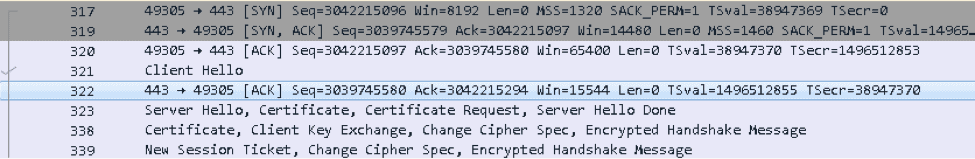
- Enhanced correlation with TCP Analysis between protocols, eg. when choosing an ACK Packet we see a checkmark next to the packet that is being acknowledged.
- More detailed scroll bar, to quickly find trouble spots within a capture
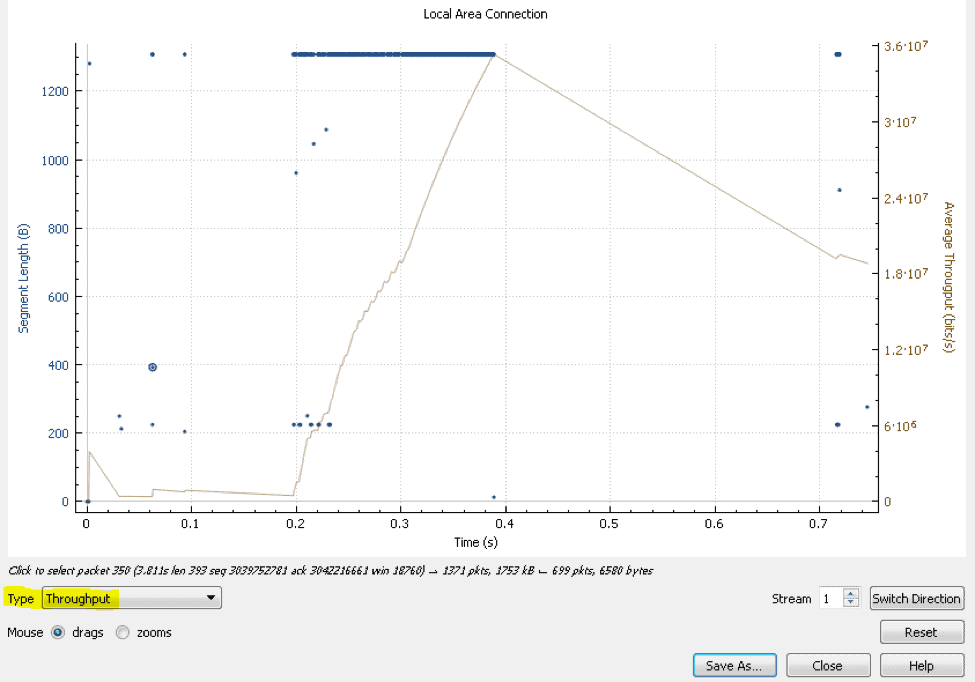
- A much more simplified and easier way to navigate graphs (Notice now we can easily switch graphs using the same window.)
All of these are great reasons to run Wireshark, however Wireshark works best in small doses.
What if we need to step up our protocol analysis game and start capturing & analyzing 100’s and of MBs or GB’s of data?
If this is something you have tried to do in the past with Wireshark then you probably know how difficult that is to perform.
Well that is where a few additional Wireshark Alternatives and Replacement tools that come in.
The best Wireshark Alternatives for Packet Sniffing
1. Site24x7 – FREE TRIAL
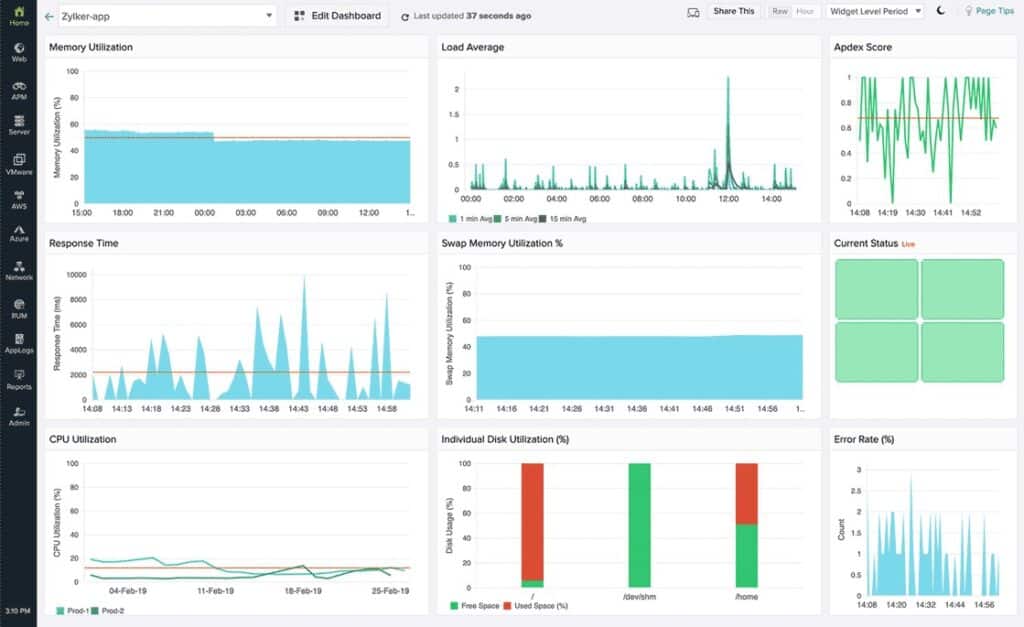
Site24x7 offers complete visibility into the network device that helps run in-depth analysis and track major performance issues. Users even gain full control over the different aspects of the network using this tool. It uses a Simple Network Management Protocol (SNMP) monitoring system to track incoming and outgoing traffic and detect anomalies in real-time.
Key Features:
- Track Network Components and Endpoints
- Threat and Fault Detection
- Traffic and Bandwidth Monitoring
- In-depth Analysis and Reporting
- Automatically device discovery
Why do we recommend it?
Unlike the Wireshark System, the Site24x7 Network Monitoring Tool gathers all the data packets itself, monitors them, and troubleshoots issues quickly. It is an all-in-one solution that helps enterprises monitor the health of each network element both at the device and interface level.
Basically, it is a robust and stable cloud-based monitoring solution that comes with a comprehensive set of features that will eventually help your business stay on top of all network issues and ahead of your competition.
With the help of this tool, users can monitor and manage the traffic flow and configurations in a single platform. Croma, CNA, and BPP are a few top companies that are currently using Network Monitoring tools for detecting issues in real-time and troubleshooting them.
Who is it recommended for?
Businesses of all sizes can use the tool for monitoring network elements thanks to its manageable price list. Even large businesses can invest in the tool and access greater capacity by paying extra.
Pros:
- The tool ensures that all your communications that take place between the server and networks are encrypted and secure
- Discovers devices automatically and maps them out for clear visibility and analysis
- Users can easily track the health, status, and performance of each network element and network traffic
- Allows setting up threshold limits and alerts on exceeding or discovering a breach
Cons:
- The tool offers more than just SNMP monitoring which might require more time to fully understand its various capabilities.
Access the 30-day free trial.
EDITOR'S CHOICE
Site24x7 Network Monitoring is the editor’s top choice for it is suitable for businesses of all sizes and can be used for tracking down every network operation and element both at the device and interface level. Users can even watch over all on-site and remote network resources with the help of this tool. These insights collected from the tool make it easier for network administrators to look into the issues with the functionality and health of network interfaces. Further, with SIte24x7, you can identify and detect threats in advance and send instant alerts updating on the status. It is a multi-vendor supporting tool that can keep a watch over your network without interruptions and reduced downtime and outages.
Download: Start a 30-day FREE Trial
Official Site: https://www.site24x7.com/signup.html
OS: Cloud-based
2. SteelCentral NetShark Appliance
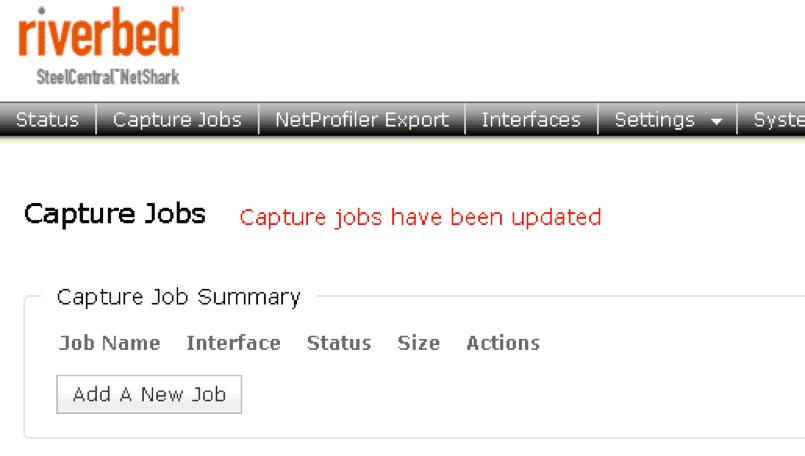
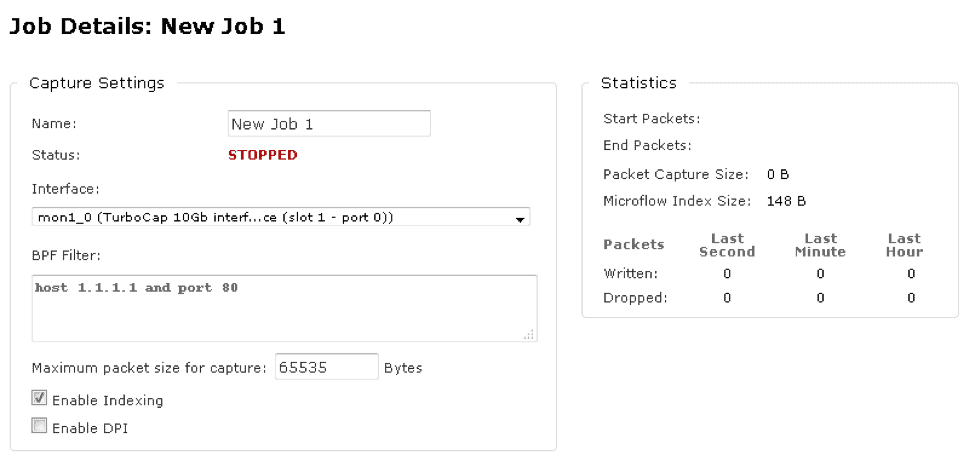
The NetShark Appliance is a niftly appliance that hangs off the network and accepts packets at high speeds with no loss for analysis later. At first glance the appliance the appliance itself can appear simple & basic, which at some level it is. After the all at the end of the day the physical NetShark appliance is a storage appliance with a very fancy NIC Card. However in my experience with the NetShark appliance, it is that level simplicity which makes the device most useful and beneficial.
See the steps below for navigating the NetShark and creating a capture job:
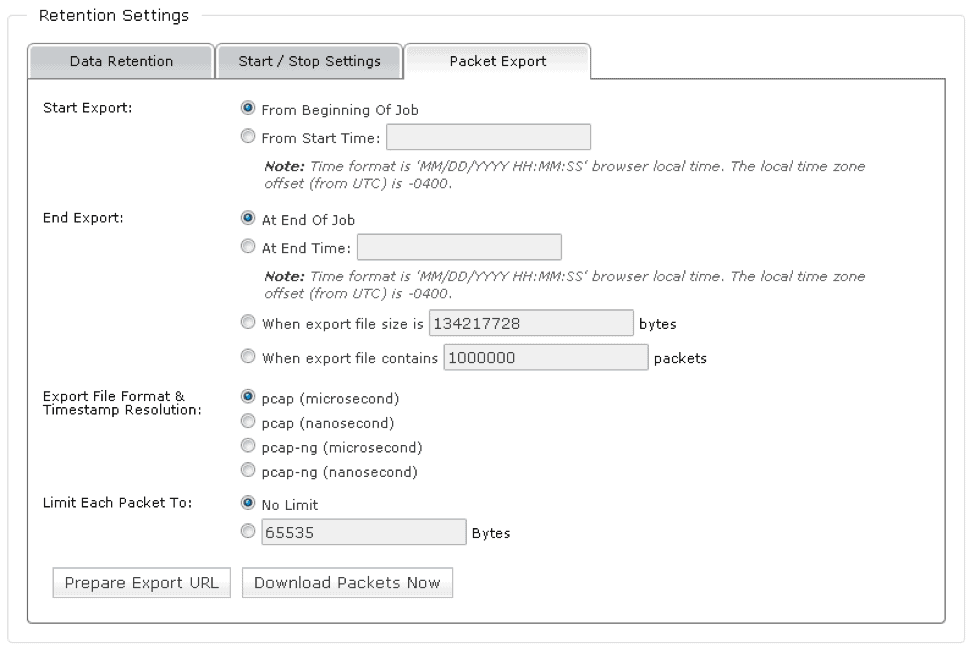
To start using the device you simply need to create capture jobs (see above), and just like when capturing traffic with Wireshark you can apply capture filters using BPF (Berkeley Packet Filter) syntax. Allowing you to have complete control and capture the traffic you need. This paired with Tera-bytes of storage make the NetShark appliance a very important tool for any network professional that needs to perform packet analysis in high performance environments.
When it comes to exporting those packets outside of the NetShark it is as easy as access the capture job and exporting the packets you want, you can even export specific timeframes.
I imagine the next question you might have is, “Now that I have all these large packet files how can I easily analyze these files.” After all, Wireshark tends to struggle with large capture files; well that is where the next tool comes in.
3. SteelCentral Packet Analyzer
Think of this tool as Wireshark on steroids. This is a commercial level tool also sold by Riverbed and accelerates in many areas where Wireshark tends to lack. To name a few:
- The ability to quickly filter through large pcap files that stop Wireshark in its tracks.
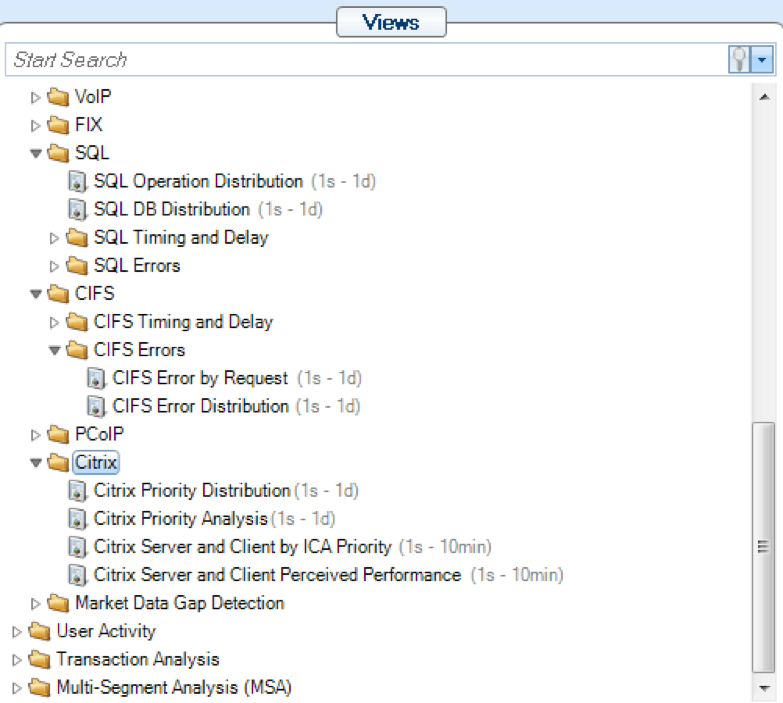
- A host of protocol specific filters allowing you to analyze anything from Citrix to SQL
- Easily identify tough to find problems by quickly filtering through timestamp information.
- Simple integration with SteelCentral NetShark so you can slice packets live from the NetShark directly from the Packet Analyzer application itself.
The one qualm I have with Packet Analyzer is that there is still some reliance on Wireshark. Once you have filtered through the packets and found the area in question you may still need to export the packets to Wireshark to see the raw packet data. However, it does show how closely knit the two applications are. One reason these applications I so closely tied is because the creator of Wireshark Gerald Combs is also employed with RiverBed working on Enterprise level tools while also supporting the OpenSource market.
For anyone that needs to perform protocol analysis in large environments, these tools will be detrimental to your success. While each of these tools might not be perfect and have their own flaws it’s when we start pairing up these tools do they really start to shine.
Wireshark Alternatives FAQs
What are some reasons to look for Wireshark alternatives?
Some reasons to look for Wireshark alternatives include the need for more advanced features, improved scalability, or better integration with other network management tools.
What are some popular Wireshark alternatives?
Some popular Wireshark alternatives include tcpdump, tshark, ngrep, and Zeek (formerly known as Bro).
How does tcpdump differ from Wireshark?
Tcpdump is a command-line tool that captures and displays network traffic in real-time, while Wireshark offers a GUI-based interface and includes more advanced features, such as protocol analysis and packet filtering.
How does the cost of Wireshark alternatives compare to Wireshark?
The cost of Wireshark alternatives can vary widely, with some tools being open source or free, and others requiring a paid subscription or license.